Privacy Solutions for Blockchain Transactions
Contrary to popular perception, blockchain transactions are not 100% anonymous. They are said to be pseudonymous. So pervasive had the belief in the anonymity of these transactions been that the earliest usage for cryptos such as bitcoins was in the Dark Web, particularly in the darknets such as Silk Road where users could use bitcoins to pay for various illicit products and activities ranging from pirated content to drugs.
The reality, however, is that many cryptocurrency transactions are fully traceable. From your bitcoin address, for example, it is possible to glean lots of information about you such as your spending patterns, income, your wealth along with information on the people that you associate with.
There are various ways in which your wallet address can be linked to your identity. If you share your wallet address publicly on forums, social media channels or even blogs, it is fairly easy to trace the address back to you.
We also leave our digital signatures behind on various platforms as we send and receive cryptocurrencies on the internet. For example, if you purchased your bitcoins or other altcoins at an exchange, you will leave behind your identity along with your wallet address which is fully traceable back to you. If you pay merchants using a cryptocurrency, they can easily make the connection between your wallet and your identity. In fact, there are companies that now specialize in linking wallet addresses to identities.
While there are a lot of tools and resources that can be used de-anonymize your crypto trail, there are equally plenty of anonymizing techniques that you can use to add layers of security to your online privacy and enhance your anonymity when using various cryptocurrencies. Here is an overview of some of the top privacy solutions for blockchain transactions:-
Bitcoin Mixer
Blockchain transactions are stored in a public ledger where anyone can access them and trace the origin and destination of transactions done by a public address. The full blockchain is publicly and freely available so it is fairly easy for someone to look at your transaction history if they have your address. They can even use this in conjunction with other publicly available information to deduce the identity of the owner of a particular wallet address. At the protocol level in most cryptocurrencies, there is no procedure that can be used to anonymize these transactions.
This is where you will need the bitcoin mixer. The main function of the bitcoin mixer is to disrupt the traceability between bitcoin addresses by mixing various bitcoins in order to obfuscate the transaction history. It does this by swapping the coins for other addresses that have the same value or through the creation of temporary blockchain addresses. Doing this makes the blockchain transactions exceedingly difficult to follow. While there are companies that specialize in bitcoin mixing and a charge a fee, there are also various peer-to-peer mixers that you can use if you are really nervous about giving away your identity.
The procedure of bitcoin mixing is known by many other terms such as bitcoin laundering or bitcoin washing. Some of the bitcoin mixing services include BITMIXER and Helix.
Disadvantages of Bitcoin laundries
- The main disadvantage of a Bitcoin laundry is that you must have a trusted service that will return the coins. Also, if you use a compromised or a malicious bitcoin laundry service, you will lose the anonymity.
BIP47 Reusable Payment Codes
The fully transparent feature of the Bitcoin blockchain as well as those of some cryptocurrencies that have not implemented native-level privacy features makes them a financial privacy nightmare. If a prying eye has your address, they can easily track the list of transactions that address has performed and the amounts involved in the publicly available blockchain ledger.
However, Payment Codes such as the BIP47 Payment Codes enable you to mask your addresses with a hexadecimal Payment Code that is untraceable in the blockchain ledger. The payment codes allow for the creation of permanent bitcoin addresses which are reusable and which can be publicly linked to an identity without sacrificing the privacy of financial transactions in the blockchain ledger. The Payment Codes serve similar functions to the Bitcoin Stealth Addresses but they are a more flexible and practical variant with different consumer-friendly features and trade-offs.
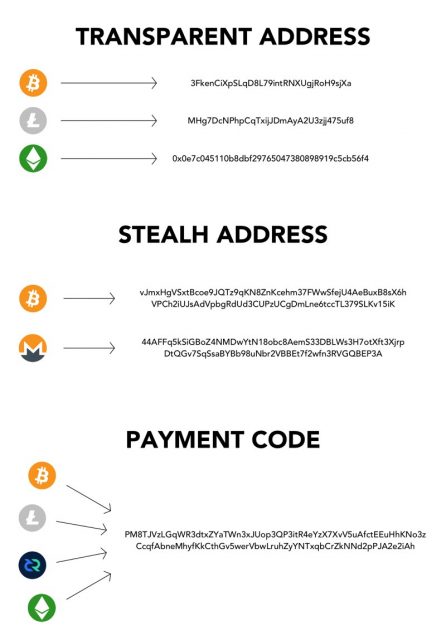
This is the idea on which the BIP47 Payment Codes is predicated. They allow a sender to identify themselves in the cryptoeconomy without leaking information (bitcoin addresses) about their financial details. On the surface, a BIP47 Payment Code looks just like any other cryptocurrency address- a long hexadecimal sequence. However, unlike the typical cryptocurrency addresses that have to be exchanged for every transaction, a BIP47 Payment Code user will only need to get the Payment Code detail of the other party once. The wallet software that is integrated with the Payment Code will subsequently generate an address every time you transact with that party.
The BIP47 Payment Code therefore becomes the “public face” masking blocks of your blockchain transactions. It takes the place of your Bitcoin wallet address. You can publish it anywhere and no user will be able to trace the underlying addresses that have been generated when making payments with your Payment Code.
The BIP47 Payment Code is also highly convenient and you can reuse the same payment code across multiple cryptocurrencies. You can use a single payment code to send and receive payments in Bitcoin, Litecoins, Ethereum etc. This is a super-cool feature that allows you to privately transact in multiple cryptocurrencies in the cryptoeconomy without the need to create multiple Payment Codes to mask your activities.
Quorum
Developed by J.P. Morgan, Quorum refers to the open source, enterprise-focused and regulated implementation of the cryptocurrency Ethereum that is used in supporting private transactions and smart contracts. It is an Ethereum permissioned (used within a group of known participants granted the permissions) version that is widely used in the financial sector. The main Quorum feature is its privacy-focus. It is used widely in applications that require a high throughput and high speed processing of private transactions that is generally the defining feature of transactions in the financial sector.

Quorum was developed to address some of the key challenges that financial institutions have faced in adopting blockchain technology. That is mainly privacy. Blockchain technology is built on transparency. Blocks of transactions are available on a publicly accessible blockchain ledger and are fully traceable. That might be OK for individual users but banks want more discretion for their clients.
The Quorum implementation aims to address these concerns by offering users better transaction and contract privacy, transaction-level permissions management and network-wide permissions management, a consensus mechanism that is vote-based as well as better speed and performance.
Although it is open source, Quorum is peer-permissioned via smart contracts so it operates as a consortium blockchain. The networks utilizing Quorum are not open to everyone. Only the known participants can gain access to the networks. Due to this failsafe, these networks can operate with higher level of digital trust. All the participants in the Quorum blockchain have to be approved by an authority.
Beyond the permissioning safeguard, Quorum offers more privacy features beyond the typical pseudonymous nature of most cryptocurrency blockchains. It does this through “private” and “public” on-chain transaction options for clients. The “public” transactions are just like your typical Ethereum transactions which take place in an unregulated environment and are easily accessible via a public blockchain ledger. The “private” transactions and contracts are however verified and the details of the transactions are concealed from the general public.
Message transfers in Quorum are done via an encrypted messaging protocol known as Constellation. Constellation is a peer-to-peer encrypted message exchange system used in the transfers of private data to the participants in a network.
This being an enterprise banking blockchain technology, it is also designed with a backdoor by default to ensure the know-your-customer (KYC) and anti-money-laundering (AML) compliance provisions are met during use.
Ring Signatures
Ring signatures are a type of digital signatures used in cryptography whereby a group of possible signers are pooled together to generate a unique signature that can authorize transactions. Each of the group members will have a private key that can authorize a transaction but it is computationally infeasible to determine which particular member’s key has been used. They are highly effective as a digital privacy tool because the anonymity that they offer is not revocable. The signer participants in a group signature can also be randomly improvised among groups of users without any prior setup.
Advantages of Ring Signatures
- It is highly effective as a privacy tool in cryptocurrencies helping hide the amounts of cash that are being sent while also masking the transactions in the publicly accessible blockchain ledger. Only a sender and recipient can know what has been sent.
- The anonymity is irrevocable. When you take a ring of possible signers, it is impossible for a prying eye to tell which of the possible signers that are part of a signer group belongs to a particular user as all the signers are equal and also valid. The transaction outputs in a ring signature are completely untraceable.
- There is fungibility: Fungibility refers to the quality of a commodity where one unit of a commodity is equivalent to any other units of the same commodity so the unit can be totally substituted. Bitcoins are not fungible because the transactions are completely traceable (the public blockchain ledger is fully transparent and accessible and transaction history is traceable). However, cryptocurrencies with ring signatures are fungible because they create an opaque blockchain where each transaction can have a plausible deniability. The history of transactions is completely untraceable. In this regard, the cryptocurrency that has fungibility is almost like real cash which is almost totally untraceable. One cryptocurrency that utilizes the ring signatures so well in its privacy protocol is Monero.
Disadvantages of Ring Signatures
- Where ring signatures are not properly implemented in the mechanics of a cryptocurrency, you will have partial de-anonymization.
Zerocoin Protocol
To address the privacy issues in the publicly accessible Bitcoin blockchain ledger, a Zerocoin extension was proposed for the blockchain that would have created greater anonymity for bitcoin transactions.
The anonymity comes about through the creation of a new crypto called Zerocoin that resides in the Bitcoin blockchain. The Zerocoins can be acquired for the base currency and later redeemed for the same. A proposed use case was whereby a user performs normal bitcoin transactions and then runs them through a Zerocoin protocol in order to add a layer of anonymity.
The anonymous Zerocoin transactions would exist alongside the public transactions in a cryptocurrency blockchain such as a Bitcoin. A user would then convert the non-anonymous currency such as a Bitcoin into the anonymous currency like Zerocoin. The Zerocoins can be sent to other users, split or merged and then converted back to Bitcoins where necessary.
Advantages of the Zerocoin Protocol
- Because it would operate in the Bitcoin blockchain network and could be implemented as an add-on through a series of extensions to the cryptocurrency protocol, Zerocoin would have been easy to deploy without the need for a central coin issuer.
- Incorporates very secure cryptographic encryption that ensures transactions are completely untraceable.
- The Zerocoin system will remain in place even if various nodes in the cryptographic system are compromised because the implementation is distributed among all nodes.
- It is possible for users to make payment with a totally new cryptographic protocol that is untraceable.
Disadvantages
- The extension was never implemented in the main cryptocurrency with the largest market capitalization-Bitcoin-and as a result, it is inaccessible to bitcoin users. However, it has been implemented in some altcoins such as PIVX and ZCash.
https://virtualrealitytimes.com/2018/04/09/privacy-solutions-for-blockchain-transactions/https://virtualrealitytimes.com/wp-content/uploads/2018/04/Quorum-Blockchain-Technology-600x326.pnghttps://virtualrealitytimes.com/wp-content/uploads/2018/04/Quorum-Blockchain-Technology-150x90.pngCryptocurrencyContrary to popular perception, blockchain transactions are not 100% anonymous. They are said to be pseudonymous. So pervasive had the belief in the anonymity of these transactions been that the earliest usage for cryptos such as bitcoins was in the Dark Web, particularly in the darknets such as Silk...Sam OchanjiSam Ochanji[email protected]EditorVirtual Reality Times - Metaverse & VR

